introduction
sqlbox is an open source C/C++ secure database access library at this time limited to sqlite3 databases. Instead of operating databases in-process, sqlbox uses a multi-process, resource-separated approach to safe-guard the database from the calling application.
some features…
- role-based access control on a per-statement and per-source (opening and closing) basis, limiting application database access and manipulation to role purview
- in-child filter capabilities allowing for selective scrambling or anonymisation of query results
-
asynchronous
mode for some operations allows all the security benefits with only the slightest performance penalty in one-way interprocess communication -
multi-select
mode allows forward-caching of step responses, considerably reducing the frequency of synchronous communication
The library is well-documented and has all of its behaviour checked with a large set of regression tests. It follows semver versioning. It may be run on any modern UNIX. It is a BSD.lv project.
latest release…
install
You'll need any modern UNIX system with the sqlite3 library already installed. (Tested on FreeBSD, Linux, OpenBSD; built on OpenBSD.) I strongly suggest using OpenBSD as it provides the pledge facility. Other systems, such as Linux or FreeBSD, are more difficult (hugely so, in the former case) to configure securely. Start by checking that your system's third-party packages system doesn't already have sqlbox. If it does not, proceed.
Download either the latest release (sqlbox.tar.gz | sha512) or the current sources from the GitHub repository.
-
Download and verify the newest release (if not from the source repository).
sha512 -C sqlbox.tar.gz.sh512 sqlbox.tar.gz tar zvxpf sqlbox.tar.gz
-
Configure for your system and install destination, compile, install.
The default is /usr/local.
./configure make make install
You may need to run this with BSD make (bmake) on non-BSD systems. You shouldn't need to pass any arguments toconfigure.
That's it! The manpages are the canonical source of information on this library. Start with sqlbox(3).
security
The purpose of sqlbox is to provide
security to your data
- only pre-set statements shall be executed
- only pre-set databases shall be opened
- database components shall not be reachable by process file-system or memory
- provide this with an acceptable impact on performance
It effects this by forked a database management process with pre-set database names and statements. Once forked, the names and statements are inherited and can no longer be changed. Communication with the database is via tightly-controlled socket IPC with the control process. Requests for statements are by identifier, not strings.
When the caller uses a constraint mechanism such as pledge, it makes the database completely inaccessable except via controlled IPC.
This security is built to enforce a role-based access control system, which is useful when a single application has several different roles of operation (e.g., users, administration, analysis). This is enforced within the management process, so a compromised application cannot change its own role except within the transition matrix set during creation. The management process also provides opaque anonymisation of data, which is especially useful for analysis when database information may contain identity information.
A full automated test suite makes sure that these constraints are followed. Its coverage is as follows:
Testing is further enabled by running with valgrind and compiler sanitisers as a commit hook.
performance
The following are a series of performance measurements between raw
sqlite3 databases.
using the
C/C++ API,
ksql,
and sqlbox.
For consistency, all databases in the performance analysis are opened as :memory:.
sqlbox tries to minimise the amount of system calls used to exchange data, and
minimise even further instances of synchronous
communication where the client requests then waits
for data.
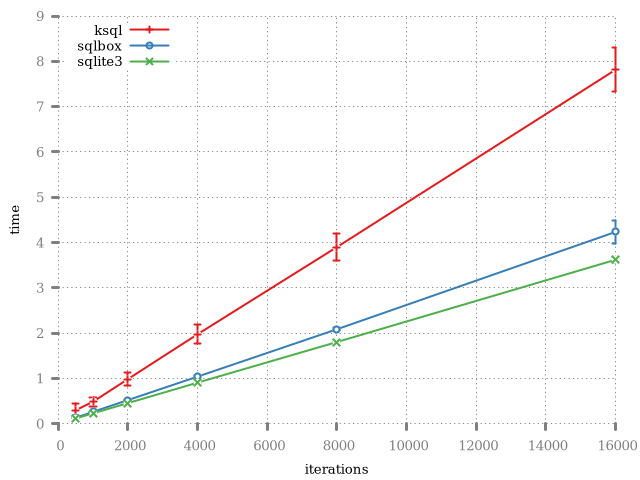
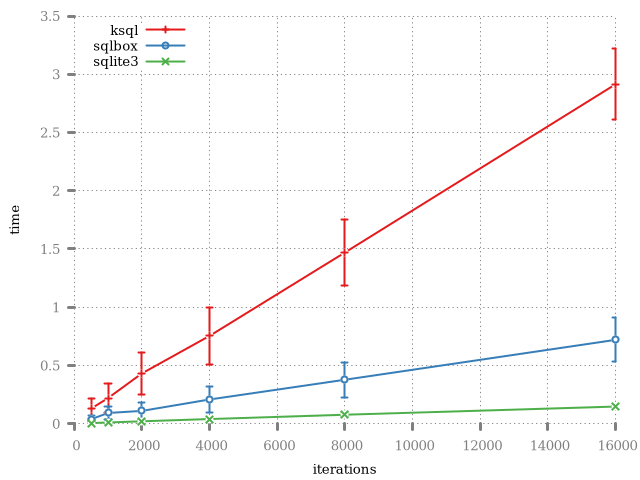
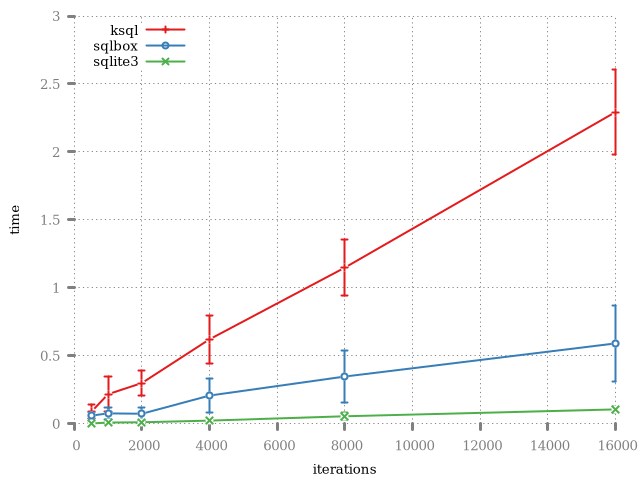
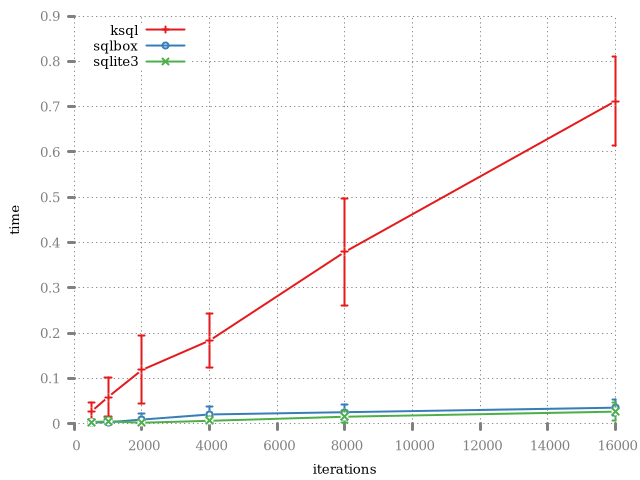
In general, the slowness of ksql is that each operation involves a synchronous read and write between server and client. In sqlbox, there are asynchronous versions of most functions to significantly reduce contention. Moreover, the wire format is optimised for one unfragmented read (or write) in the general case.
documentation
The canonical documentation for using sqlbox is its manpages. Below is a list of all bundled manuals. These apply to the current version of this software, which is 0.2.1.
This library makes use of pkg-config, so testing for installation, compile and link flags, etc., are all accomplished using that way.